Image by g4ll4is used under creative commons license
American politics is an extremely divisive issue and I will not be taking any sides in this debate. The purpose of this article isn't to promote any sides but rather to talk about how encrypted communication tools are being used.
Michael Moore launched a sub-page to his domain called Trumpileaks. The purpose is to give whistle blowers a "secure mechanism" to share information.
The website recommends a bunch of encrypted messaging apps to share information via the web or by traditional mail. It recommends the use of Signal, Peerio, WhatsApp, Encrypted Email (Protonmail), traditional mail or general email if you just don't care.
These tools are very good for general secure communication but not if you are trying to "hide" from the american intelligence community. All of these tools leave a crumb trail of meta data which can be tracked back to you and the fact this isn't mentioned is irresponsible (my opinion).
What follows is not an exhaustive operational security guide (OPSEC) but just general recommendations.
Protecting your network access
The first thing you will want to do is protect your network identity, which would be used to narrow down a list of suspects when trying to identify you.
Connect from free WIFI
The first recommendation is to use free open WIFI in a location away from your normal living areas (home, work, etc). Chose a place that is relatively far away like a coffee shop. Before using it to leak info, make sure you visit it looking for cameras in and around the area. When visiting it do not buy anything or leave any trail you were here.
Remember that your cell phone is a beacon that broadcasts your location constantly and turning it off doesn't work. Either leave it behind or place it in a cell phone blocking Faraday cage bag (buy or make your own). You must block your signals before leaving your house.
I recommend going to your end location using public transit (since your car can get tracked via license plate or in-car navigation). Pay using anonymous transit tokens purchased with cash.
Use an anonymous VPN
Once you have found a good location, you will need a VPN device like the Invizbox (review here or you can buy it here. Since you will use this once, I recommend buying one with 2 months of VPN access. Invizbox allows you to buy via Bitcoin so do that. Make sure you setup a non trackable one time use bitcoin wallet for this transaction and ship the device to a fake name/fake location (so it can't be tracked back to you).
Set up the Invizbox a couple of days before using a secure machine (described later), at another anonymous WIFI location using fake information.
Use a service like Fake Name generator to help you create your fake identity.
When setting up your Invizbox Go, use their VPN service to connect to a location like Switzerland. but do not use their TOR service.
How to buy anonymous bitcoin
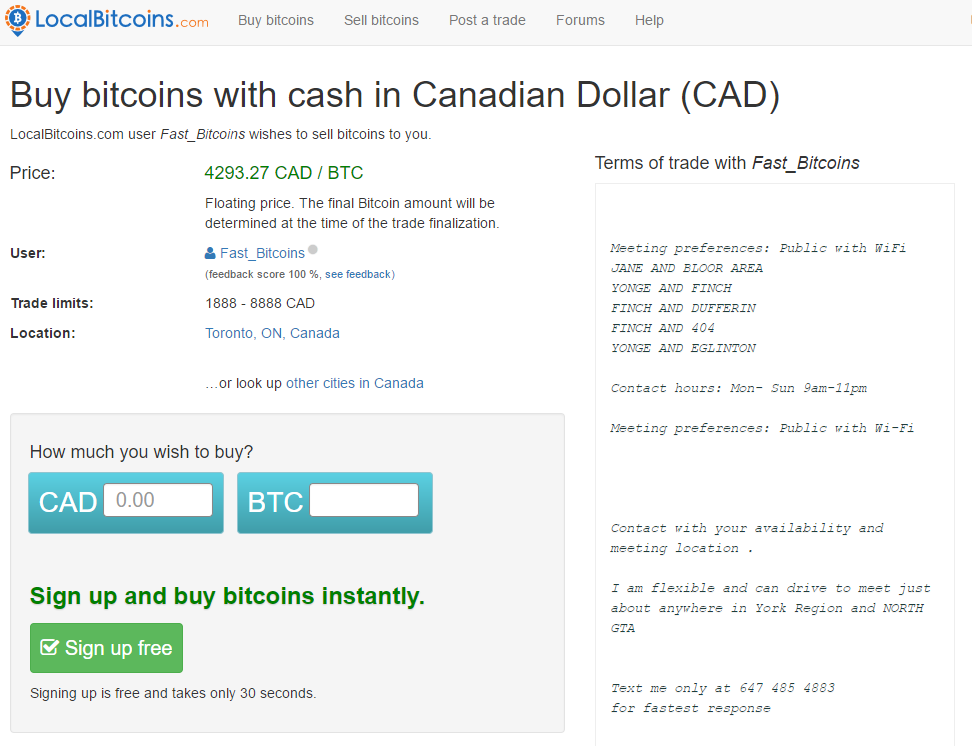
Cash is king but for some transactions you may need bitcoin. You can use a site like LocalBitcoins to find a local Bitcoin trader that will allow you to pay cash and stay anonymous.
I am not endorsing this trader, I am providing this as an example only.
Keep transferred amounts small so as not to arouse law enforcement interest (less than $500 per transaction). Use a disposable cheap android phone to host your bitcoin wallet and load only 1 identity on it.
Create a fake identity that cannot be traced back to you. Buy burner phones cash.
Remember, making one mistake will cause your anonymity to fall.
Protecting your Operating System
Use a secure Operating System with TOR
Your computer can be compromised to leak your identity. Even without being compromised, it leaks your identity all the time. Not only do you leak data but the unique setup of your computer leaks your digital fingerprint to any site that wants to track you (article here). If you want to test this yourself, check out Panopticlick.
Hopefully you now agree that traditional operating systems aren't secure enough for the purposes of anonymity. You will need an Amnesic Incognito Live System called TAILS. This is a free operating system that you boot from a USB key that is fresh everytime you use it and doesn't leave any forensic traces on the machine it was used on.
Tails also routes all internet traffic through TOR or I2P (use TOR). So you will use the Invizbox Go to tunnel to Switzerland and then you will use Tails with TOR to get to the dark web.
Tails is built for privacy and has a specially designed browser to minimize tractability. Ensure you follow the instructions to double check the integrity of the file you download. You will then need 2 fresh USB keys to built the final Tails USB bootable system.
You will have to make sure you laptop is compatible.
Protecting your transmission
Secure email
If you are going to use email, then make it as secure and anonymous as possible. Use a free Potonmail account (review here) via TOR.
Anonymize your style - Stylometry
Well funded threat actors and nation state intelligence are able to identify people using stylometry. This is a technology that analyzes your writing style and then uses this knowledge to de-anonymize your content on darknet sites.
Think of stylometry as a digital fingerprint built against your writing style (how to evade stylometry) . You may also want to checkout the Anonymouth tool from The Privacy, Security and Automation Lab (PSAL) Drexel University, Philadelphia PA.
Using Anonymouth will allow you to engage online while minimizing the intelligence community's ability to perform stylometry on you.
Michael Moore should setup a TOR SecureDrop service
The best way to send information as a leaker is to use a TOR service hosting SecureDrop (create by internet privacy advocate Aaron Swartz). It is an encrypted dead drop used by journalists to collect info from whistle-blowers while protecting their identity.
The Freedom of Press Foundation has taken over the project since Aaron's death and helps media organizations install and run the tool. the FPF is addressing all of the shortcomings of the original tool
Don't trust printed leaks
You may be thinking printing and mailing is the best option but it isn't. Many printers have a hidden feature which adds invisible identification to every printed page (see EFF article here). These "invisible" yellow dots allow intelligence agencies and police to track down which printer printed a document. Recently this technique was used to track down an NSA leaker when a picture of a leaked document was show by The Intercept and the NSA found out the document was printed on one of its documents.
If you are interested, you can read about this technique here.
Conclusion
Simply following the basic instructions on the Trumpileaks website is irresponsible and dangerous. Ask yourself what would be the impact if the leak was tied back to you? Are you willing to live with the consequences?
Even with strong knowledge and good security hygiene, perfect anonymity does not exist on the internet. If you are determined to leak, learn how to do it and take the above precautions but know there is always a risk you will be discovered.