This is an opinion piece.
TikTok is a Chinese social media network that allows creators to publish short videos. It started with a ton of slapstick comedy and karaoke but has since matured with much more diverse content. It has become one of the most popular social media platforms because of its powerful video pairing algorithm. It has an incredible ability to show you a continuous stream of content you will find interesting, and it is usually correct.
You can see samples on their trending webpage without needing an account.
TikTok belongs to a large Chinese company called ByteDance. This is problematic for western politicians because (it is suspected) Chinese corporations have been stealing IP from their western counterparts for decades.
But why is the USA talking about banning TikTok (a rare censorship move by the US government)?
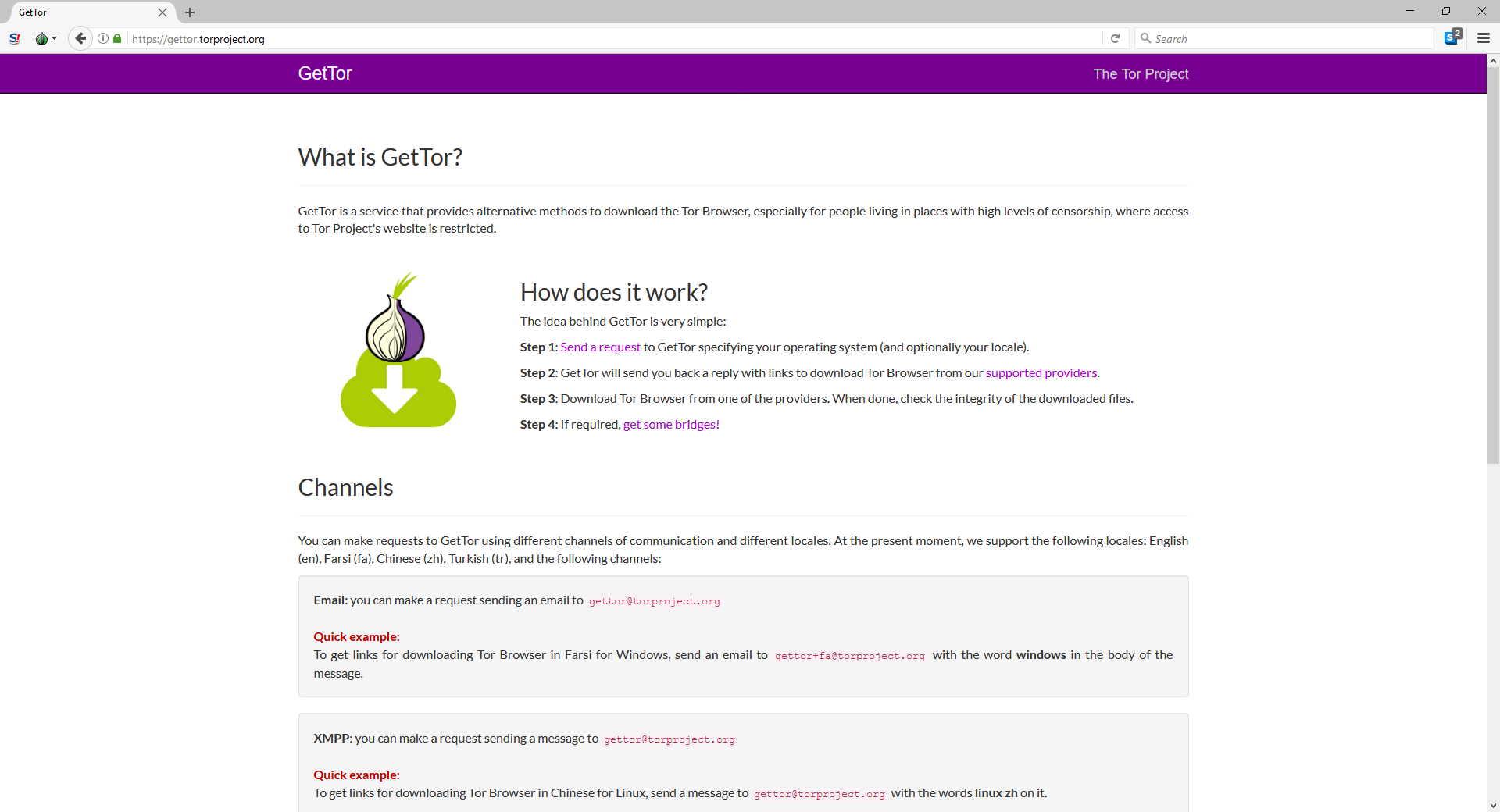
It is important to remember that China has banned most western social media apps within its borders. Without working around the great firewall of China, a citizen cannot access Facebook, Twitter, Reddit, or any Google property. It banned them to stifle conversation, to censor free speech and to monitor its citizens.
You can use a website like Blocked In China or Comparitech to check if a site is accessible from China
I have lived in Hong Kong and worked in China for a considerable amount of time. So I hope that I can bring some interesting perspectives about China and this TikTok discussion.
The first thing to remember is that you cannot evaluate this matter through an American lens.
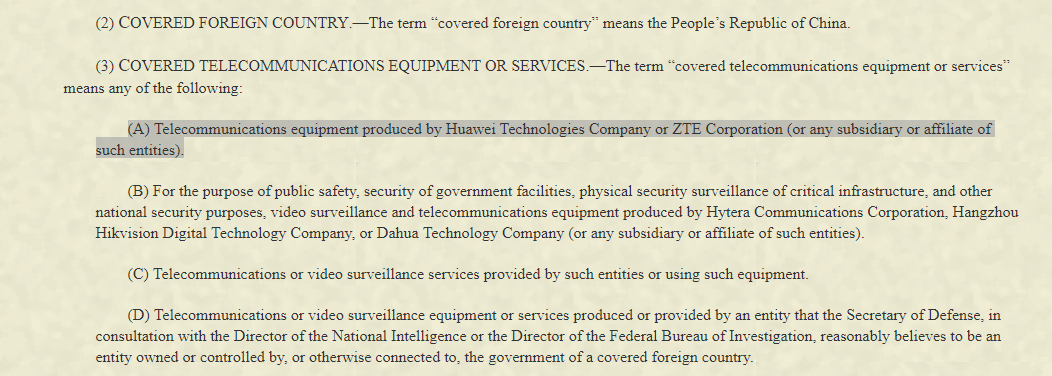
Every medium-sized company or larger (think larger than 50-75 employees) is beholden to the Chinese government. This means that the Chinese government can seize, capture or use any information held by any Chinese company. Unlike US authorities, they do not need a court order to undertake any of these activities). Even though the Chinese government has allowed companies to operate with a semi capitalistic model, they theoretically own all Chinese companies operating in China.
A more risky point is (it is said) the fact that the Chinese government incentives Chinese companies and citizens to expand internationally and sign partnerships with western organizations to steal IP. The goal (it is said) is to use this knowledge to build a Chinese variant. Once perfected, the end-goal is to export this Chinese version overseas and take over that market (this works in every vertical from clothing to aerospace).
Read about their 14th five year plan here. Think of the five-year plan as a master blueprint for their economy. It lists the industries they want to lead in during that five year period. The next one (2021-2026 will cover the environment and green tech). During those five years, they want to become industry leaders at any cost (remember the IP theft claim above).
If you watched Silicon Valley on HBO, they alluded to this characteristic when Jìan-Yáng "borrowed" American company ideas to start copies in China (time-code 0:44).
Sometimes patriotic hackers could also attack foreign companies to aid China. The US Department of Justice pinned the Equifax hack on 4 Chinese hackers. This hack gave hackers ,and (it is said) the Chinese government, access to the credit records of millions of Americans. They also had access to confidential Equifax business processes.
So what?
Let's summarise
every Chinese company is owned by the Chinese government
The Chinese government has access to all the data these Chinese companies have
So considering the above, prima facie, Tiktok should be a national security threat. Last year American senators "woke up" and asked their national intelligence agencies for analysis.
Obviously, Tiktok pushed back by saying that they use American servers running in the USA. TikTok also appointed an American CEO.
Think of all the data these companies collect about you (name, location, social graph, habits, likes, etc.). Used "properly" it can generate a ton of obviously useful and some less obviously useful data points.
Read my 2014 article about how Target predicted its’ customers were pregnant before they knew it by data-mining their buying habits. Now imagine what could be done with a ton more information.
Regardless of where the data sits, the company that owns TikTok is ByteDance, a large, fully Chinese organization. Even if the data sits in the USA, ByteDance (it is believed) cannot refuse a request from the Chinese government (regardless of where the data sits).
Remember that Chinese employees have access to the American servers and data. It is claimed that ByteDance has ties to the communist party back home. All of these simply bring TikTok closer to the Chinese government and make obtaining information that much simpler.
In addition to concerns about China gaining access to traditional social media users’ data, there is the concern of TikTok being a tool to exercise soft power.
A popular tool used in cyber offensive activities is Psychological Operations (PsyOps). The goal of a psyops program is to secretly fuel the fire in a foreign country's population to take actions desirable to you.
We heard about TikTok users coordinating on the platform to troll Trump's Tulsa rally.
Was this truly a grassroots movement, or was a foreign adversary secretly working in the background to encourage actions aligned with its interests? Remember that a good psyops program is secret and almost impossible to identify.
Americans see TikTok as a bastion of free speech, but it isn't. Many have claimed Tiktok removes other types of videos that would not normally be considered bad in the west:
TikTok Is Reportedly Removing Videos of People with "Abnormal Body Shapes"
TikTok 'tried to filter out videos from ugly, poor or disabled users'
We have heard other complaints about videos critical of China also were removed. I don't know if this is true, but it would be consistent with how we believe China operates. Don't forget China uses TikTok to flex its soft power by encouraging creators to publish pro Chinese content.
This goes back to the original point of not evaluating TikTok with your American lens. Whereas the removal rules for videos on Youtube, Facebook or Twitter are relatively well accepted (harmful, child abuse, exploitation, promoting hate, etc.), Chinese rules for removal of content are very different. China has an ambiguous law that aims to “prevent the spread of rumours”, What constitutes a rumour is purposefully vague and this law has been used to shut down dissenting voices. When watching online complaints about the types of videos actually being taken down, it seems more aligned with enforcing this law to protect the Chinese “face”.
My assessment is that the Chinese government doesn't care about users discussing American politics. They want to ensure no one criticizes China, the Chinese system or the government's authoritarian rule. This is exemplified by TikTok deleting a video by a makeup channel. She talked about the plight of the Uyghur while doing her makeup and had her video deleted.
China believes in free speech as long as it doesn't impact them or their narrative of the world. Try searching TikTok for videos discussing Hong Kong independence, Taiwan independence, or anything else criticizing China.
Here is a shocking trend for you. Teens in the US and Europe that believe they may have been shadowbanned will publish videos with the Chinese national anthem playing in the background, with pictures of Xi Jinping and professing their love for China. Even though this is being done mockingly, doing this enough could have unintended psychological consequences and start creating positive associations in these teens about China.
Conclusion
I am anxious to see if the USA will ban TikTok and on what grounds. Will they conduct a full and impartial review, or will it simply be a decision of political convenience. Don't get me wrong, as a security professional; I don't trust any company based in China that is beholden to the Chinese government. The general public making dance videos may not care that their data could be used to build a profile of each user.
That if the Chinese government wanted, they could use the videos to create a sizeable facial recognition database with a robust social graph.
That this data, merged with other data from other breaches and leaks, could help build a reasonably reliable profile of hundreds of millions of people.
That the platform could be used to sway younger voters in a particular political direction more aligned with Chinese interests.
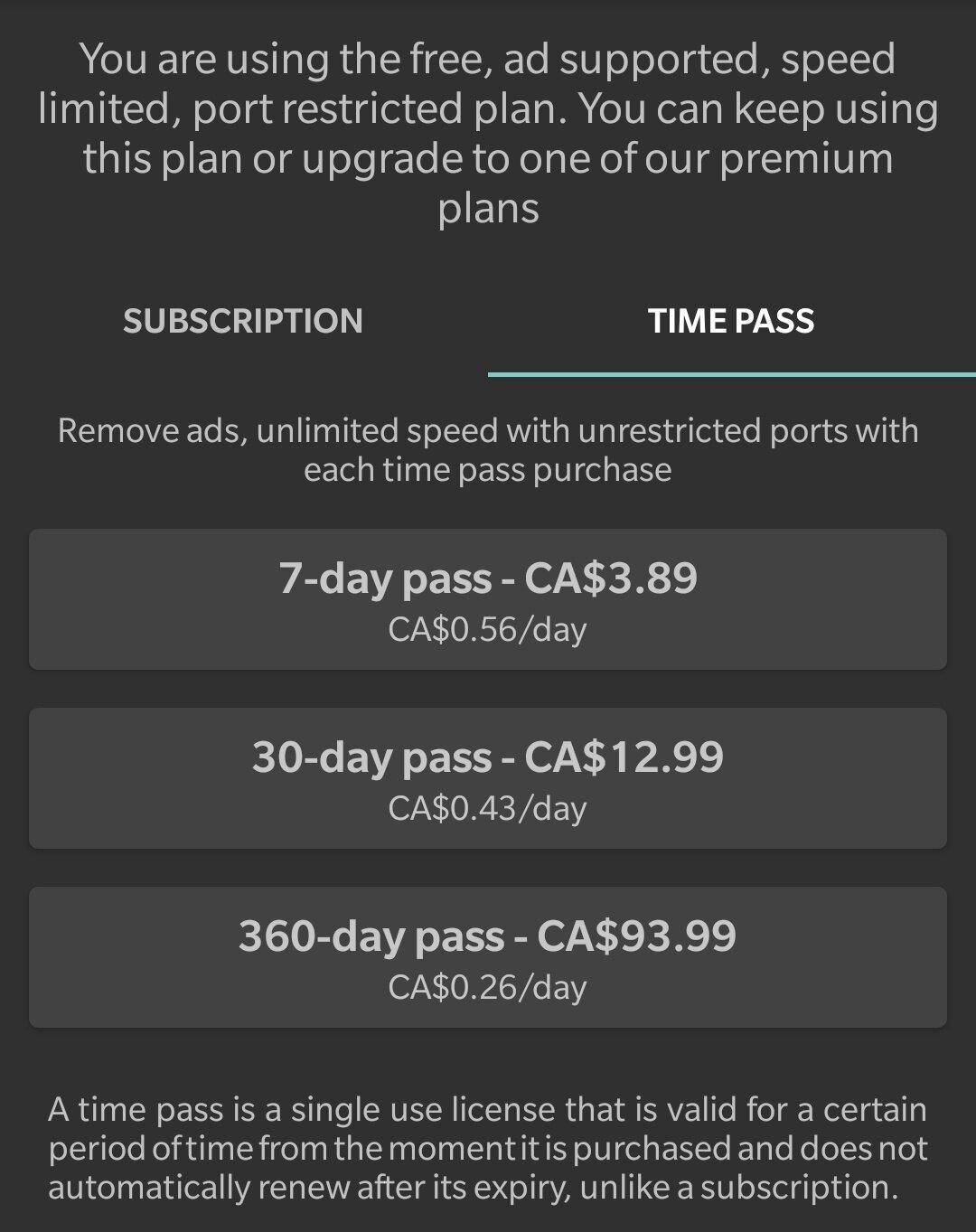
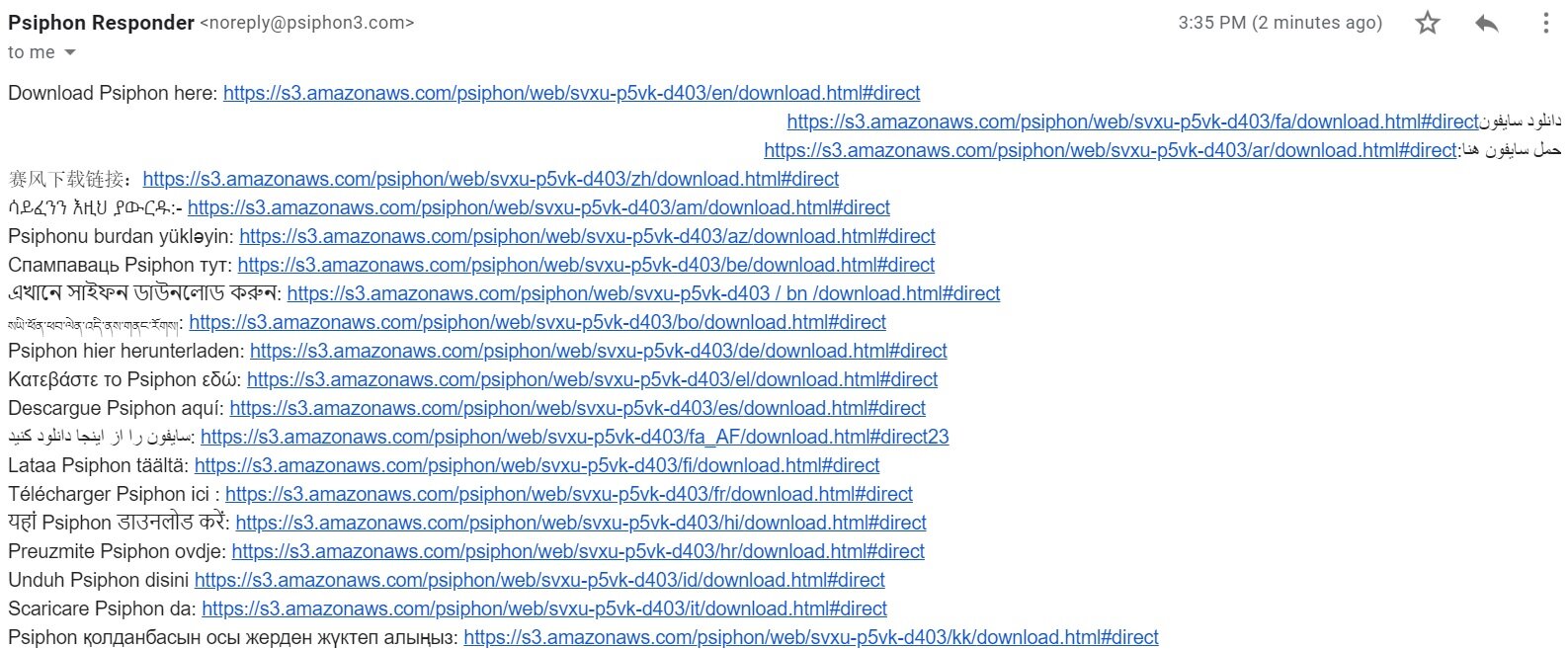
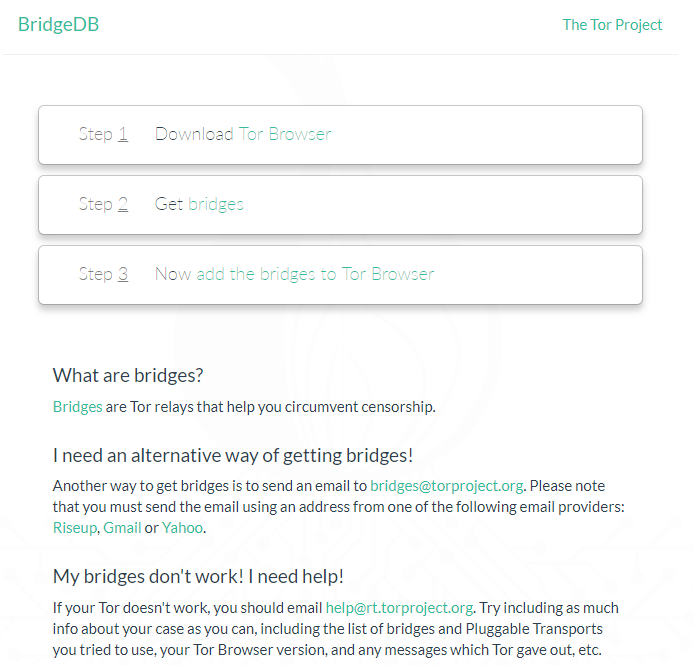
I am curious about how the US would implement a ban? Even if they mandated the appstores remove the apps, Android users could sideload it, or TikTok could build a Progressive Web App (a web page that looks and acts like an app). We simply don’t have the same censorship tools as China.
I don't know if the platform IS a risk to national security, but I personally don’t trust it.
If I start seeing more "Chinese contraband" content on TikTok, then I will be inclined to believe they are independent of the Chinese government. I want to see
videos about the Muslim minorities being sent to re-education camps
videos asking for freedom to be restored in Hong Kong
videos talking about Taiwanese independence
videos criticizing the communist government
videos discussing he persecution of Falun Gong members (even imprisonment)
Until then, I hope users understand what could happen with their data. Particularly parents of younger children. Once something is uploaded to the internet, it can never really be removed.