A profile picture is one of the most important elements of your social media profile. It's the first thing people will see when they visit your page, and it's a good way to make a strong first impression.
That being said, not all profile pictures are created equal. Each social network has its specific requirements for what makes a good profile picture, and failure to follow these guidelines can result in a less-than-ideal image that doesn't represent you in the best light.
Here are some tips for taking a great profile picture for each of the most popular social networks:
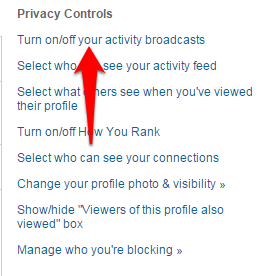
LinkedIn: Your LinkedIn profile picture should be a professional headshot appropriate for a business setting. Avoid casual or overly-stylized photos, and make sure the background is simple and free of distractions.
Facebook: For Facebook, you can go with a more casual photo than you would on LinkedIn. However, it's still important to avoid anything that could be seen as too staged or artificial. A good rule of thumb is to choose a picture that you would be comfortable sharing with your friends and family.
Instagram: On Instagram, your profile picture should be an image that represents your personal brand. This can be a photo of you engaged in a hobby or activity that you're passionate about or something that showcases your unique sense of style.
Snapchat: Snapchat is all about fun and spontaneity, so your profile picture should reflect that. Don't be afraid to get creative with your snapcode (the image people use to add you to the app). You can even use a funny or memorable picture from a past event as your profile pic.
Twitter: Since Twitter is all about brevity, your profile picture should be an image that can be easily seen and recognized in a small size. A simple headshot or logo is usually best for this social network.
Remember that your profile picture is an important part of your online presence, no matter which social network you're using. Take the time to choose an image that represents you well, and you'll be sure to make a great first impression on everyone who visits your page.