Phishing is a powerful and effective tool and a favorite in the threat actor arsenal. So what happens when your cloud provider gives threat actors a roadmap to steal from you?
A couple of weeks ago, Workday sent a security advisory to its customers regarding a phishing campaign targeting its customers. Although details of the attack campaign are light, here is what I believe is happening based on discussions on various darknet forums.
What was the Workday phishing attack model?
First, none of this is a weakness or vulnerability in Workday or any of its systems or processes. The threat actors send an email to employees, pretending to originate from a high ranking executive (CFO, CEO, SVP HR, etc.) and are asking, asking them to log into "Workday" to fix an issue. This fake Workday site harvests the credentials which then allow the threat actors to log in and change direct deposit accounts for employees thus stealing money.
Based on reports I have seen, these emails are professionally written (so they do not contain the telltale signs of being a scam) and are currently not being caught by many large spam filtering services.
How did Workday facilitate this attack?
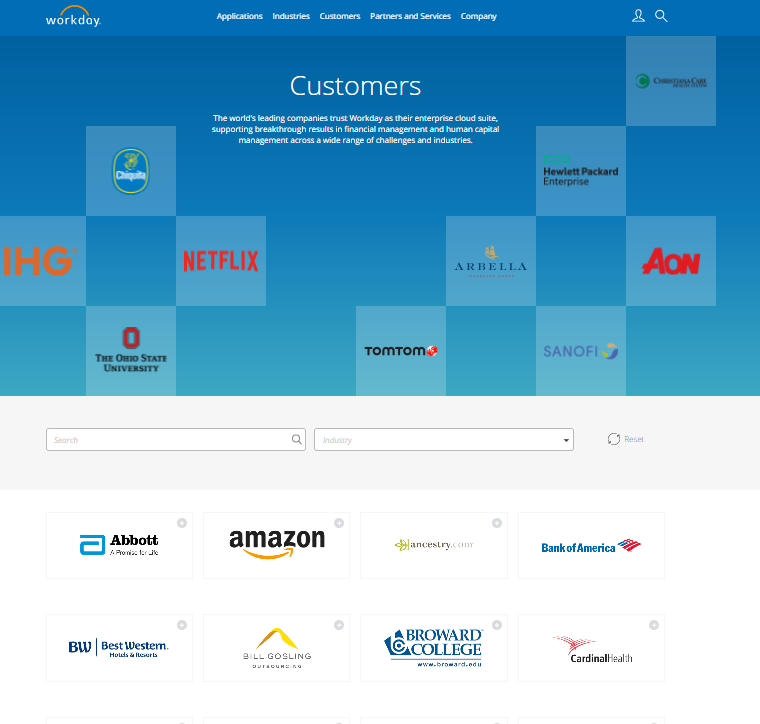
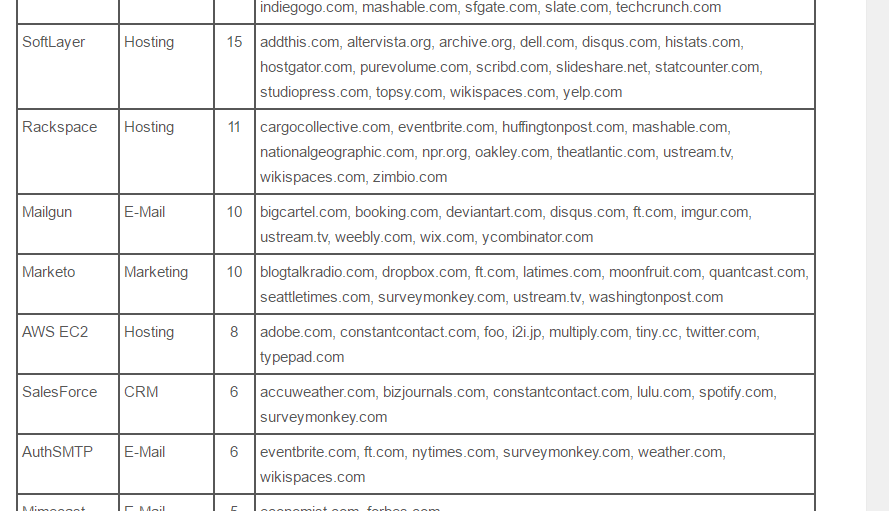
Like many SAAS and cloud service providers, Workday proudly displays a ling list of satisfied customers on its webpage. This marketing list basically becomes an attack plan for these threat actors by knowing exactly which customer to target with which SAAS provider name and which attach to use.
Security is a balancing act. It always has been and always will be. Ultimate security means severely reduced usability and no marketing. More marketing and usability means less security.
Security is a balancing act
Marketing is tasked with growing the business and nothing helps more than social proof (aka showing others that have made the same decision you are thinking about). The fact Workday marketing is publishing hundreds of customer names on its website is aligned with their objective of supporting business growth. After all, why should marketing avoid using all of the tools available to it just to protect the business from some attack that may or may not occur?
Even if marketing hadn’t published an exhaustive list, they probably would publish a press release when a new big-name customer was signed. This means a determine attacker could build his own list of high-value targets. Right?
As an example, they published this press released in April entitled “Workday Continues Momentum in Canada.” This wonderful piece of marketing includes this section: