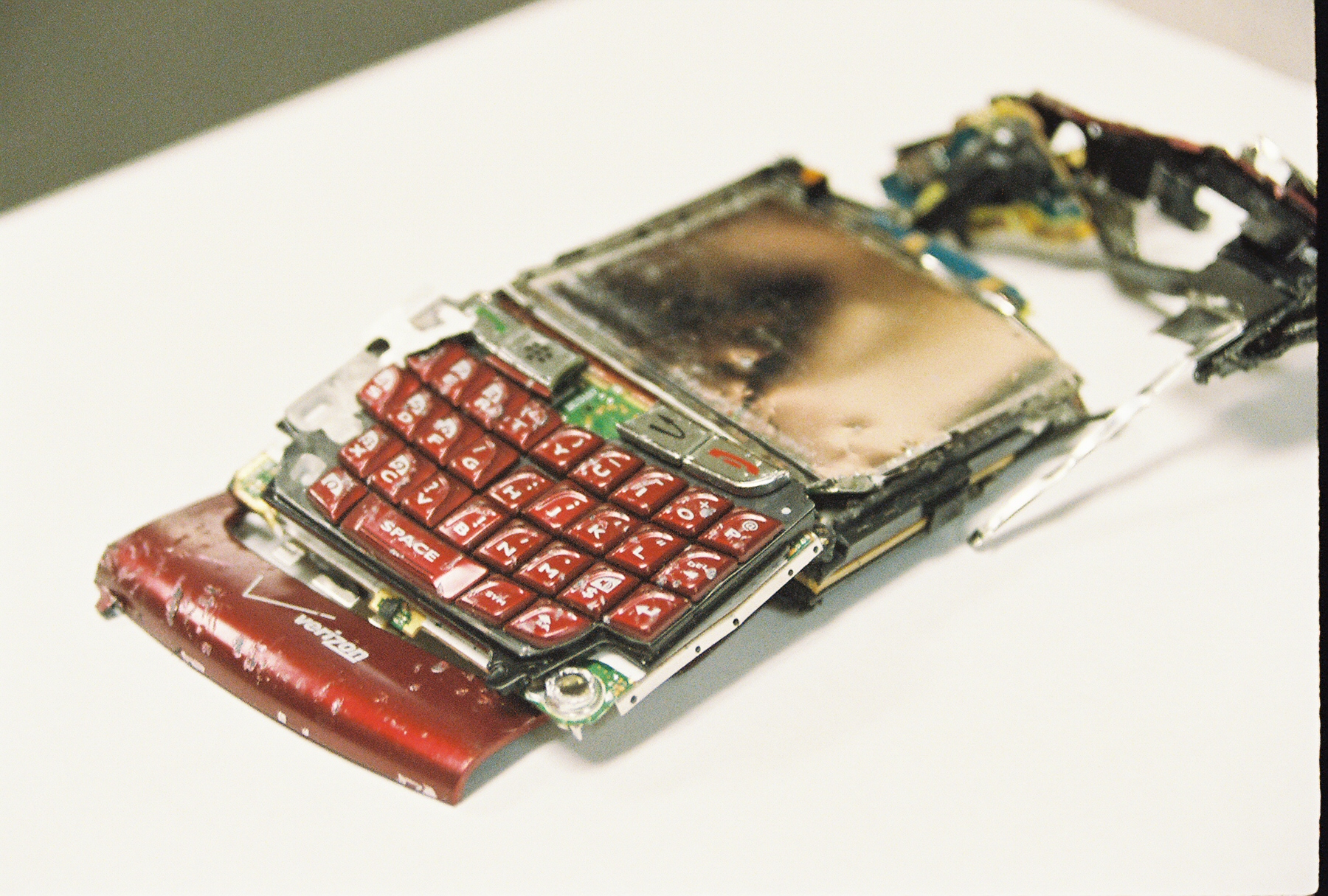
Image by Matthew Hurst used under Creative Commons License
In the above 2015 presentation, security researchers broke the secrecy around a protocol called SS7 and explained how a technically proficient user can "break it" and easily compromise your mobile phone call data and text messages. Seeing an opportunity, 60 minutes produced a popular segment that scared viewers and I still receive emails from readers asking if this is "a real thing".
Let's take a look at this together.
What is SS7?
SS7 is short for Signalling System 7 and is a carrier interconnect technology that allows one mobile carrier to connect to another and send calls and SMS to each other. It allows allows you to roam on another carrier's network when travelling. It is an old (1975) technology developed before the world went security crazy and thus is has much more basic security built in.
What can hacker access?
A skilled hacker can use SS7 to gain a huge amount of insight into the victims use of a mobile device. It will allow him (masculine being used for simplicity) to listen in on phone calls, forward phone calls, collect call metadata, ability to intercept SMS messages and ability to track the phone.
Think of all sites using SMS as a second factor authentication tool. Any bank, social network or other site using SMS to authenticate users are jeopardizing your security. Always choose another authentication option (other than SMS).
No one would be surprised if a government performed these types of tracking activities but SS7 makes it possible for anyone to do this.
Am I vulnerable to the SS7 hack?
Anyone using a smartphone (anywhere in the world) is vulnerable to the SS7 hack when using traditional mobile phone service (phone calls, SMS messages, etc),
How can I protect myself from the SS7 hack?
If you don't use traditional mobile phone services, your information can't be hacked with SS7. The only way to protect yourself is to use alternatives (which in most cases are better anyway).
As an example, instead of sensing plain SMS messages, you an encrypted messaging service like WhatsApp, Apple Messages, Google Hangouts/Allo, or any other encrypted messenger. To be clear, each of these has its own security issues which can lead to compromise but they are immune to the SS7 attack.
What about phone calls you ask? Many of the above text messaging alternatives also provide voice calling services which would also be immune to SS7 hacking because they use an encrypted data channel instead of the traditional mobile phone voice system. My favorite encrypted calling app is still Signal (which was even endorsed by Edward Snowden).
Preventing phone location tracking is more complicated. Anytime your phone is on, a network operator can track your location using triangulation. The only option here is to turn it off and maybe even store it in a Faraday cage bag (like the ShieldSak which I will review). A less abrupt technique (good but not perfect) is to turn off connectivity to the mobile network and only use WIFI.