Image by Iván Rivera used under Creative Commons License
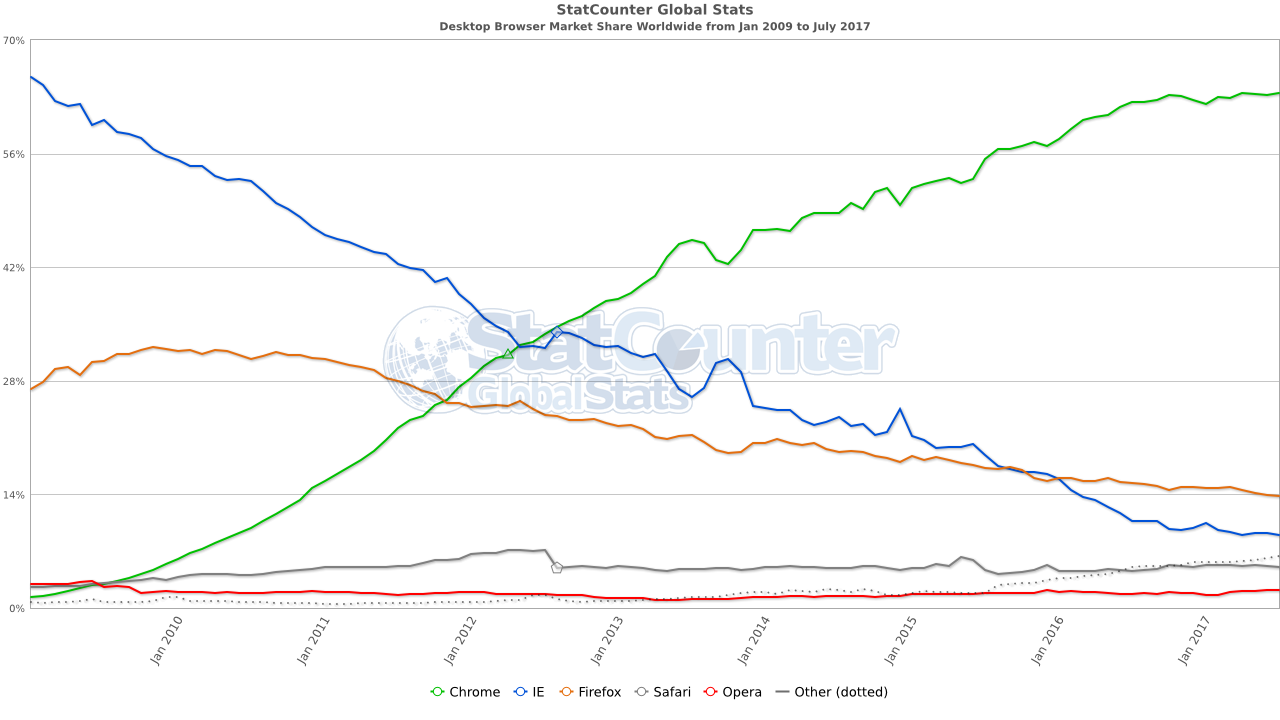
Chrome has been the browser king for many years and many users can't remember a time where Firefox was "the browser". Chrome overtook Firefox and Internet Explorer(according to StatCounter) in November 2011.
Statcounter browser marketshare
But recently a group of highly technical security experts seem to have moved back to Firefox. Why have technically knowledgeable users left Chrome for Firefox?
Battery life
Users are increasingly choosing mobile devices (laptops and convertibles) instead of traditional always-plugged-in personal computers. This means battery life is important. In a 2016 battery shootout, Microsoft aggregated billions of data points from real world Windows 10 users and found that Microsoft Edge and Firefox were much gentler with battery consumption.
Image owned by Microsoft Corporation
“These numbers are from actual Windows 10 (version 1511) use “in the wild,” not artificial tests or hypotheses. ”
Privacy
Everyone using Google products should know that the sultan of search is monitoring everything you do on the web, on its search page and in its browser. If you have never visited the Google Dashboard, you really should. It will show you all of the information El Goog has collected about you. Remember that it then uses this data to build a profile about you and we all know how powerful these predictive models can be :
Unlike many unscrupulous sites that track you without your knowledge, Google is a model citizen and clearly, let's users know what it is collecting and why. Most users are willing to trade their behavioural information in exchange for free google services (e.g. Photos, search, Gmail, etc). I think this trade is perfectly acceptable as long as the user understand what he/she is giving up in exchange for these free services.
Some people believe Google knows too much and where possible, try to use no-Google alternatives (DuckDuck Go for search, ProtonMail for email, SpiderOak One for online storage, etc).
Open Source means anyone (with the right skills) can audit the code and make sure nothing nefarious has been secretly inserted.
The fact Mozilla is not trying to become this massive financial behemoth is a comforting reality.
Browser security
To be clear, Chrome is an excellent browser and has slightly better security than Firefox but on the privacy front, Firefox wins.
There is an annual security competition called Pwn2Own and the 2017 browser compromise competition presented some interesting findings.
The Microsoft Edge browser proved to the least secure browser, having been compromized5 times. Then came Safari on Mac which was compromised 3.5 times (a half point was awarded because they had fixed one of the attacks in a beta build). Then came Firefox with 1 compromise and Google Chrome had none.
Firefox is certainly a relatively secure browser with a healthy bug bounty program but Chrome is just 1 step ahead. If you want the most secure browser and are willing to give up privacy, choose Chrome. If you want good enough security with much better privacy, pick Firefox.
Tab handling
There is no perfect browser.
Google's Chrome browser is the king of standards compliance. It is very secure since it has strict sandboxing. Each browser tab creates a new browser thread in the OS, which means a crashed tab doesn't crash the entire browser. These "features" consume a substantial amount of RAM. If you are one of those users that live in your browser and regularly has 20-50 tabs open, you probably live the sluggishness daily.
Firefox is "as fast" as Chrome but much more configurable. It consumes less RAM per open tab thus is often a better solution for users that live the multi-tab life. The flip side is that a bad tab can crash the entire browser but this is very rare.
Extensions
Chrome is the king of extensions. Just browse the Google Chrome store and be amazed at everything your browser can do.
In many cases, your most used extensions will be natively available either platform. As an example, Lastpass and UBlock Origin are natively available for Chrome and Firefox. You can also install the Chrome Store Foxified add-on which will allow you to install Chrome extensions from the Chrome store into Firefox.
In this example, I picked the Google Keep extension. When you visit the Chrome Store with the Google Chrome browser, you see this window to install the extension:
When you visit the same page with Firefox and the Chrome Store Foxified add-on, you see this window and the ADD TO CHROME is replaced with ADD TO FIREFOX
I have tested this functionality with a dozen extensions (HTTPS Everywhere, Ublock Origin Extra, Grammarly, etc) and all of them work perfectly as if they were running in Chrome. Before people start sending me hate mail, I know these have Firefox native versions but I wanted to test the Chrome extension functionality in Firefox.
Interface design
Both Chrome and Firefox have adopted a clean, minimalist approach. From the interface perspective, neither one really pulls out ahead as a leader.
Verdict
When there is competition, the consumer wins. This is true in the browser market. The extreme competition between Chrome and Firefox means both products have improved over the last 12 months.
Both browsers are relatively secure. The main difference boils down to privacy and tab handling. If you are someone that always keeps several dozen tabs open, then you may find Firefox more responsive and less likely to bog down your computer. Additionally, Firefox is a much better choice for consumers looking for more privacy.
Ultimately I think most users will end up with both browsers on their devices and use different browsers for different purposes. Recently I have started to move more of my day to day browsing back to Firefox and am satisfied. I want to encourage diversity and even chose to donate to Mozilla. Encourage not-for-profit groups powering open source software is an important step in maintaining a healthy diverse and competitive computing environment. I also donate to Tor, Ubuntu, Wikipedia and Whonix.