To provide its agents with a safe and secure means of communicating with each other without being tracked, the US Navy developed the TOR project. TOR stands for "The Onion Router." TOR sends your data via a network of nodes, or "onions," each of which encrypts your data before forwarding it to the next node. Consequently, it is challenging for anyone to trace your data back to you.
The TOR project is now managed by the TOR Foundation, a not-for-profit organization. TOR Foundation is devoted to researching and developing free and open-source software for privacy and anonymity. Individuals and organizations donate to the TOR Foundation, and governments and foundations provide grants.
TOR addresses are used to disguise your actual IP address and prevent tracking of your online activities. TOR addresses are composed of random letters and numbers, making them virtually impossible to guess. Your traffic is routed through the TOR network when you access a website using a TOR address, which makes it very difficult for anyone to determine your real IP address or track your online activities.
TOR is not just used by hackers and drug dealers but also by ordinary users. TOR may interest anyone who wishes to keep their online activities private. TOR is a very secure network, and the data is challenging to trace. There is much technology behind TOR, but it is a highly effective method of preserving the privacy of your data.
It is possible to deanonymize TOR users.
It is, however, a challenging task. The data transmitted through the TOR network is encrypted, and each node in the network only knows the IP address of the previous node and the next node. As a result, it is challenging to trace the data back to its original owner. Nevertheless, in rare instances, law enforcement has been able to deanonymize TOR users.
Law enforcement can deanonymize TOR users in several ways. An example of this is by exploiting vulnerabilities in the software that is used to access the TOR network. It is also possible to determine which nodes in the network are being used by the same user by traffic analysis. It is, however, challenging to deanonymize a large number of users using these methods.
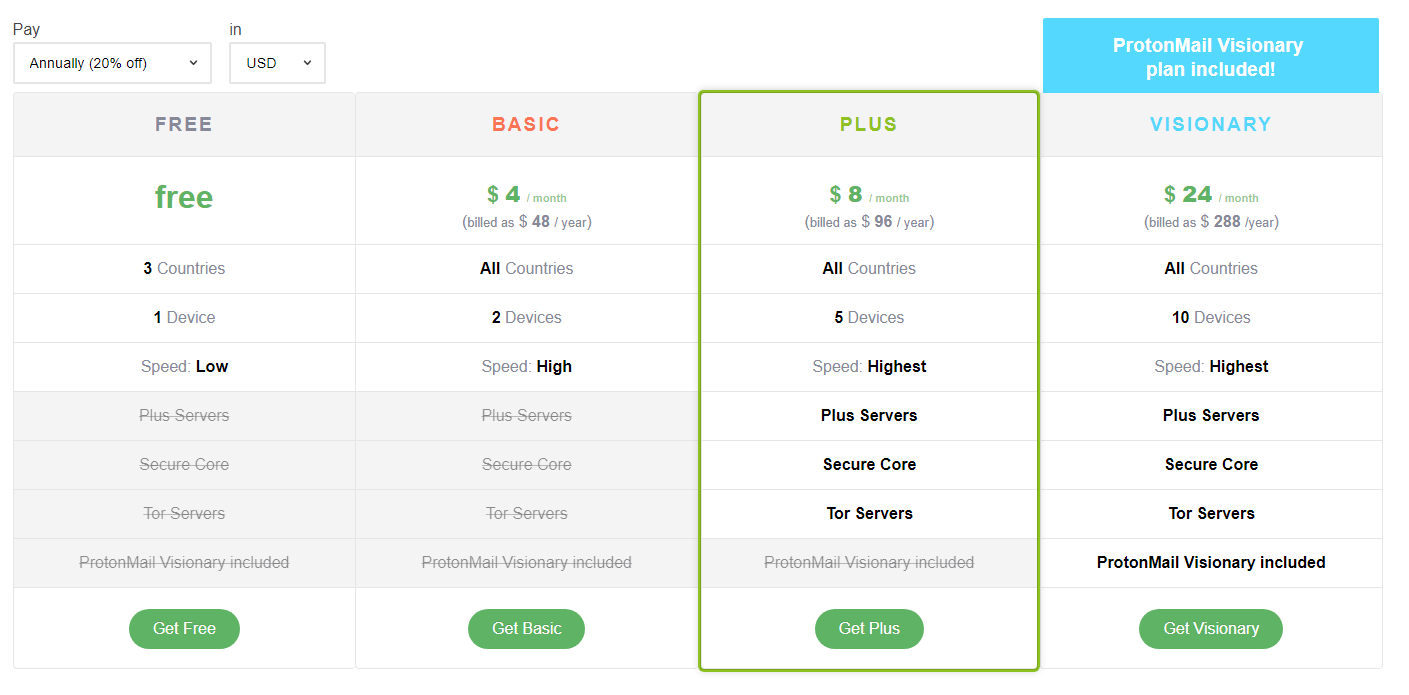
To prevent being deanonymized, there are a few steps you can take. First, ensure that you use the TOR software's most recent version. Additionally, you may use a VPN or other anonymizing service in addition to TOR. By doing this, law enforcement will have difficulty deanonymizing you. Last but not least, you should be careful when sharing information online. Be careful not to post anything that could identify you, and be cautious about the websites you visit.
TOR is constantly evolving, and new features are continually being added.
What are the most significant drawbacks of TOR?
One of the most significant disadvantages of TOR is its slow speed. In addition, since your data is being routed through multiple nodes, each node must encrypt and decrypt your data. Furthermore, TOR is sometimes blocked by websites and Internet service providers. Some internet content may be difficult to access as a result.
What makes Tor more secure than a traditional VPN?
Since TOR uses a series of nodes, or "onions," to encrypt your data, it is more secure than a traditional VPN. Consequently, no single individual or entity has access to your entire flow. Tracing individual traffic on the TOR network back to a single individual is challenging. In contrast, a VPN operator sees all your traffic since it passes through their system.
What is the relationship between TOR and the Darknet/Darkweb?
The TOR network is not synonymous with the Darknet. TOR can be used for both legal and illegal purposes. Darknet is a small portion of the internet that can only be accessed through special software, such as TOR, and is frequently used for criminal purposes.
In addition to Tor, what other networks offer privacy and anonymity?
In addition to TOR, a few other networks provide similar levels of privacy and anonymity. These types of networks include I2P, Freenet, and ZeroNet. Despite this, TOR is by far the most popular and widely used of these networks.
Keywords: TOR, anonymity, online privacy, Darknet, VPN, I2P, Freenet, ZeroNet.