Our smartphones are so much more than just internet access devices. They have become extensions of our brains. They remember our friends' contact information; they help us shop; they know where we have been and where we are going.
But what happens when someone gains access to this treasure trove of ultra-private information? I have written about how you can make your iPhone more secure here. This article will provide a handful of easy-to-implement tips.
In dots we trust
You may have noticed tiny coloured dots (green and orange) showing up on the top of your screen (upper right-hand side).
A small orange dot means your microphone is active, while a tiny green dot indicates your camera has active. The purpose of these dots is to notify you can something may be watching or listening to you. If you are on a call, this is perfectly normal, but a little investigation may be warranted if you aren't actively using any apps.
Remember that you can change what apps have access to your camera and microphone by going to Settings > Privacy > Microphone or Camera. You can then turn off access on an app by app basis.
Peekaboo i see you
There are situations where your iPhone application must have your precise location, like when navigating with your GPS app of choice.
There are other times when the application doesn't need a precise location, like looking for restaurants in a given area.
If you go to Settings > Privacy > Location Services and then click on an app, on the bottom you will see a switch for Precise Location. Turning this off will only deliver an approximate location. This is useful for apps that you have to use but are worried they are collecting your location information and probably sharing it.
A weather app is a good example of something that doesn’t need your street level accurate location and where an approximate location would be just as good while improving your privacy a little.
Accessing your photos
There has been an incredible amount of discussion in online forums about Facebook using the metadata of your photos to build a more complete profile of you and they probably aren’t the only one. Your photos show where you have been and who you have been with. So make sure only app that truly require photo access are given it and then only to selected photos.
To change which apps can access your photos, go to Settings > Privacy > Camera
For apps you have granted photo access to, it is important to choose which photos the app can access:
None
All Photos
Selected Photos
To change this setting, go to Settings > Privacy > Photos, choose an app and then choose what level of photo access you want to grant. As an example Instagram for me has “selected photos” only and if I want to upload a photo, I change the settings to give it access only to that photo.
Local network access
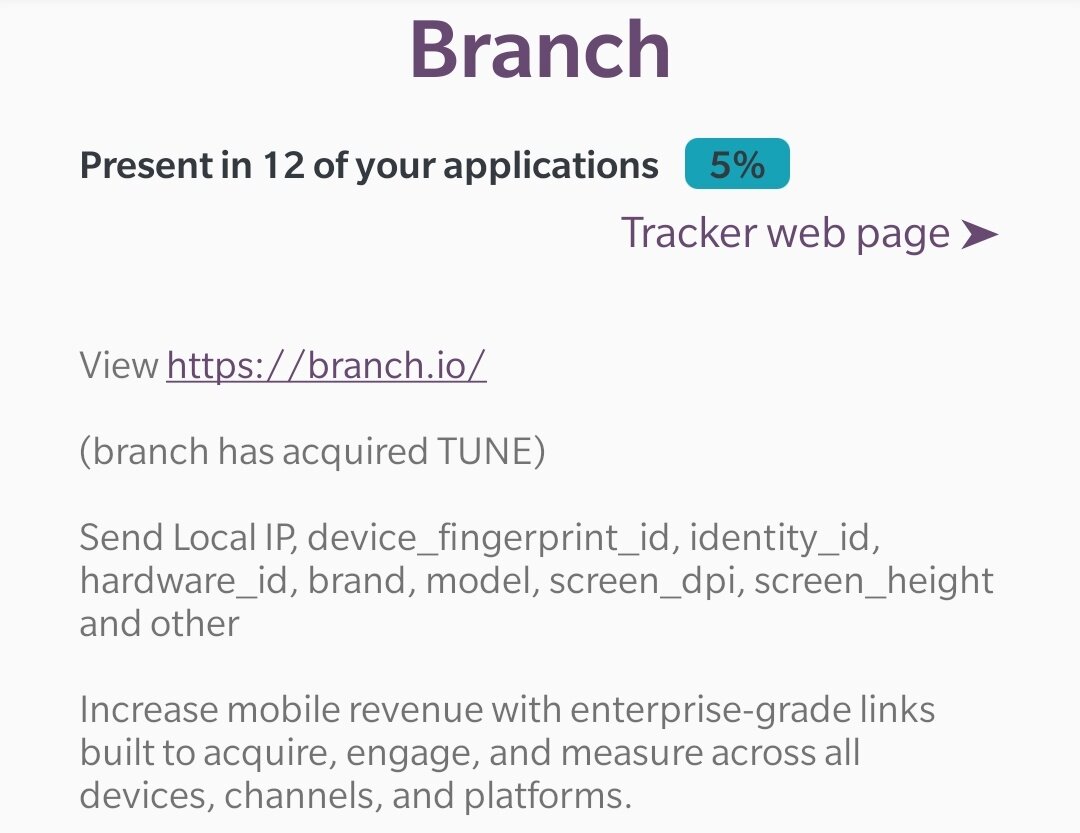
With IOS 14, you have probably seen a message pop up asking you for permission to search your local network. If you are using an entertainment app that needs to cast content on a TV or a smart home control app, asking for this permission makes sense. You have likely seen this request from apps that that had no logical reason to request this permission and hopefully you denied them this request. This is one way apps will try to identify you by collecting information about your local networks.
You can find the configuration for this setting in Settings > Privacy > Local Network . Here you can see which apps you have granted access to this right and you can change the setting at any time.
As an example, Uber Eats asks for this permission yet there is no reason to grant it access to inventory my local network. Whereas my VizioTV app has a need for this permission so it can find my device.