Image from the Cellebrite website
Cellebrite is an Israeli company that specializes in tools (hardware and software) to break cell phone security. The Universal Forensic Extraction Device (UFED) is their most popular product and it can extract info from a wide variety of cell phones in minutes. Needless to say, law enforcement loves Cellebrite and has made them a very wealthy company.
Cellebrite confirmed being breached and 900 GB of data was taken (which we believed contained end user licensing information). Cellebrite was quick to point out that passwords or payment information was not taken.
The hackers have published the dump which includes source code and customer information but also more importantly exploitable vulnerabilities for IOS, Android and Blackberry.
Cellebrite's UFED uses many of these vulnerabilities to extract the information its customers want from locked or otherwise protected devices.
Motherboard spoke to world renown IOS security expert, Jonathan Zdarski, who said the IOS vulnerabilities are already commonly known and therefore nothing earth shattering. The Blackberry vulnerabilities haven't been released yet and those will be interesting.
Obviously Celebrite is continuously updating its products with the latest vulnerability discovery so it is safe to assume this won't damage their thriving business with law enforcement.
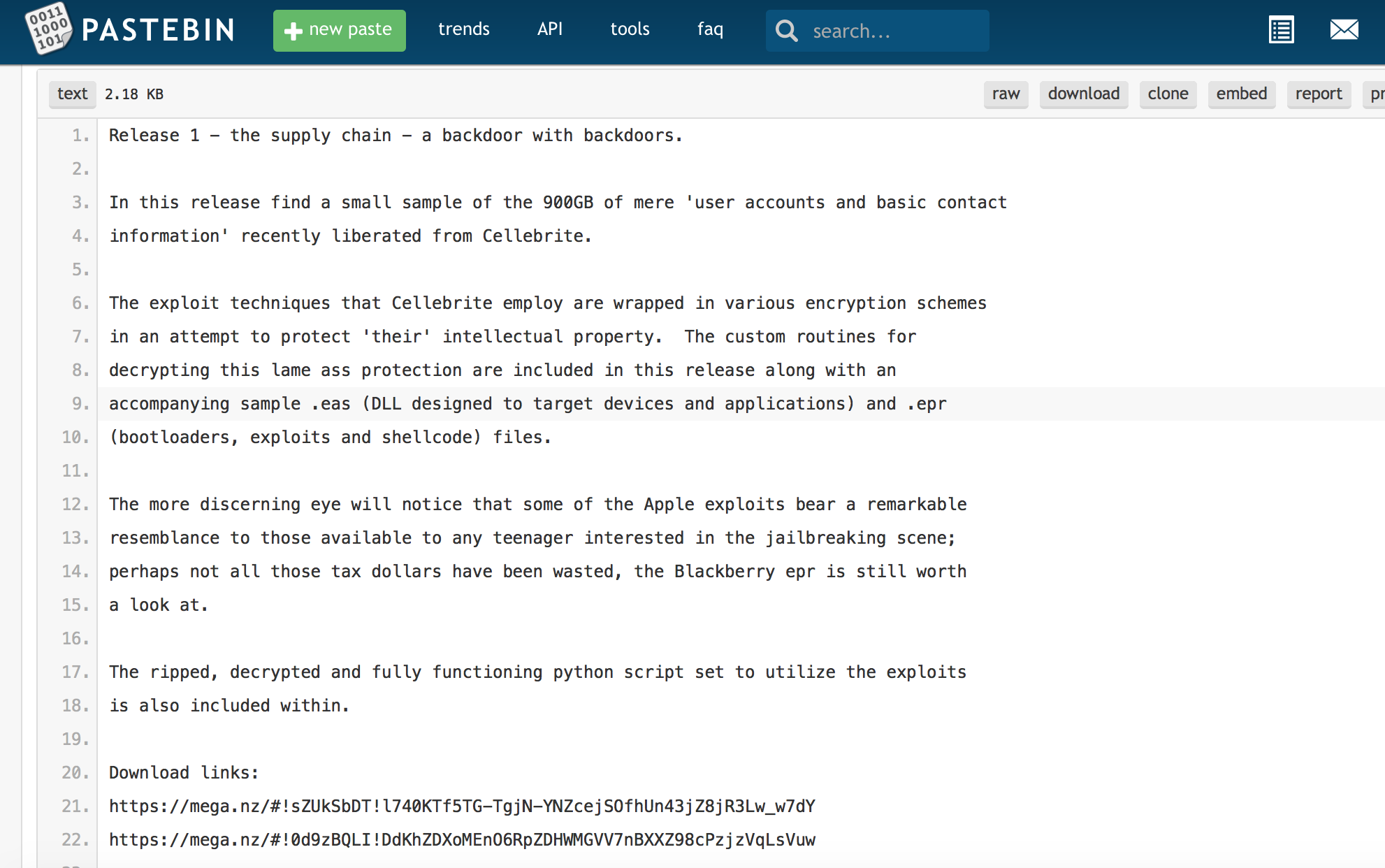
You can see a small sliver of the 900GB on site pastebin site (which will quickly disappear of course.)
The links to download the first parts of the dump are here:
https://mega.nz/#!sZUkSbDT!l740KTf5TG-TgjN-YNZcejSOfhUn43jZ8jR3Lw_w7dY
https://mega.nz/#!0d9zBQLI!DdKhZDXoMEnO6RpZDHWMGVV7nBXXZ98cPzjzVqLsVuw
These files may be taken down anytime so... Your Mileage May Vary.
The hackers are promising to released another small sump with files retrieved "via the weaponized Cellebrite update service deployed on MS Windows based devices and desktops"
“Analysis of the compression and obfuscation employed by Cellebrite on products supplied to British MOD juxtaposed with the protection free versions supplied to SOCOM and others is also included within.” added the hacker.”
The hackers are hacking the hackers. Let's see how this story unfolds.