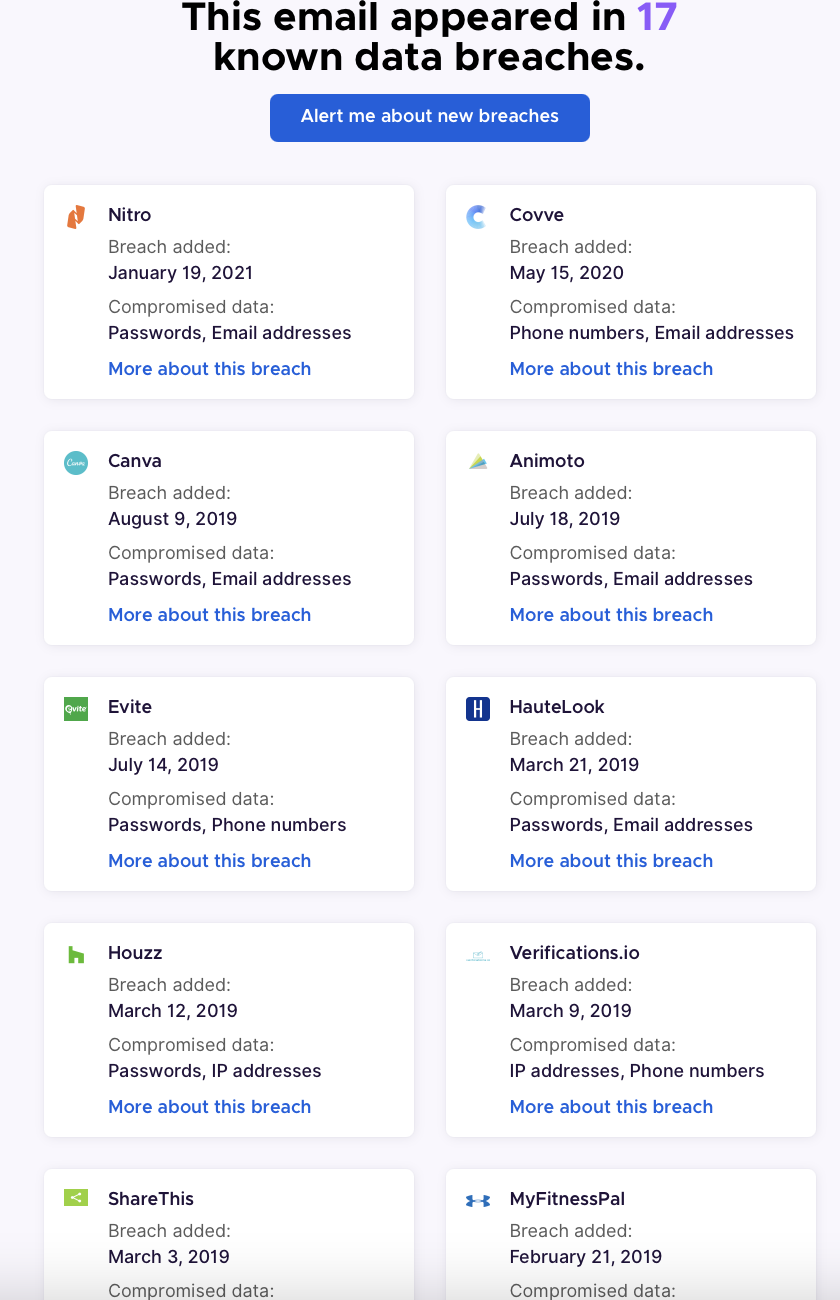
Unlike the others, this one does not provide a list of the breaches (or number) your information was found in. This could be a good third check.
I recommend checking these sites monthly or using their auto-alert feature, which will email you if your information is found in a future breach.
BIG IMPORTANT WARNING:
If these sites do not find your information in a known breach, it does not mean you are safe. There are probably hundreds or thousands of breaches that occur each year that go unannounced and therefore these sites cannot catalog that information. Always be careful and we will provide some extra insight later in this article.
Be aware of weird account activity
As mentioned above, not being included doesn’t mean you are safe. So always be vigilant with your online accounts. Sites or services with good security controls will detect anomalous activity related to your account and will email you. As an example, if you receive a password reset link, that you didn’t request,
Or if a site emails Askin if you have logged in from a location you didn’t log in from (you log in from the USA but the email says someone from Prague attempted to log into your account). Gmail does this (for unusual browsers, IP addresses or geographic locations).
Sometimes when accounts are taken over, the attacker will change the registered account email so if you try to log into a service you are registered for and it does not recognize your email address, that is an indication your account was taken over.
Another indicator is strange configurations in your email accounts. Attackers want to get into your email because that is how they can reset service account passwords or delete alerts so you are not tipped off they are trying to break into your account. They can either set up filters in your email (to forward emails of interest to them or mark alert warning emails as read and immediately delete them) or they can set up forwarding of your emails to another email address they control.
The main issue is password reuse
The main issue is password reuse. Most users have a handful of passwords they reuse for all the sites they register on. Once an attackers finds that password, they will try logging into other major services (Facebook, twitter, Instagram, Gmail, Hotmail, etc) and will have immediate access.
This is why I recommend using long unique passwords for each site and storing those passwords in a reputable password manager.
My favourite password managers (free and paid)
five sites to help you generate long, complicated and unique passwords
What do I do if my information was leaked in a breach?
With the quantity and size of breaches, it is likely that your information was leaked in a breach, what do you do now?
If you reuse passwords, then the first thing you should do is visit all the sites you use and immediately change the passwords.
If you are locked out of your account (if could mean the attackers have done an account takeover), use the reset password functionality to change your password.
If you are sure you had a registered account but the system can not find your email address (when you use the above reset feature), it could mean the attackers have changed the registered email address for your account. You will have to contact the support team for the site in question and explain the situation.
Another interesting recommendation you don’t see often is to use multiple email addresses. If you are using a password manager (and you should be by now), then why not create a free email address for different groups of services. Maybe one for online shopping, one for social media, etc
Good internet password hygiene
Use long, complicated and random passwords for each site. Something like f%[_8s9f579o+*38zjURqjK}GQZ
You can also use long passphrase (if you are stubborn and don’t want to use a password manager) but make it unique for each service: 1l0v3*K1nG!*Appl3?P3acH%Umrellas-P1nk!
Most sites use a technique called hashing to store user passwords. This means that they don’t store your password but a mathematically derived result and hackers have to “crack” the hashes to reverse them back to passwords. This cracking function is done with trial and error and is impractical for long and complex passwords. So even if your data is leaked in a breach, they may not be able to reverse the hash and your account may end up being “safe” if you use long and complex passwords.
Never reused a password for multiple sites.
whenever possible, use two factor authentication to add additional security to your account.
There is a great free site called twofactorauth that has an exhaustive list of sites that allow users to leverage 2 factor authentication and even provide a link to the info page on how to turn it on for many of those sites