Anytime you connect to a public (aka not your own WIFI) network, use a VPN to protect your traffic.I won’t discuss which VPN to choose here but stay away from free or very cheap VPNs.
If you aren’t paying for the product, you are the product.
Chose a solid well known provider whose policies and practices have somehow been reviewed.
You can run TOR to secure your traffic but that will be too slow and cumbersome for most users.
Secure backup and cloud
August 31, 2014, hackers released tones of celebrity personal photos and videos (many naked and pornographic in nature). This event was called the fapening and this was made possible because the icloud accounts, used to back up those photos from the smartphones, had been compromised. We don’t believe Apple was compromised but the attackers somehow managed to find the usernames and passwords for these users. Another reason you should enable two-factor authentication now.
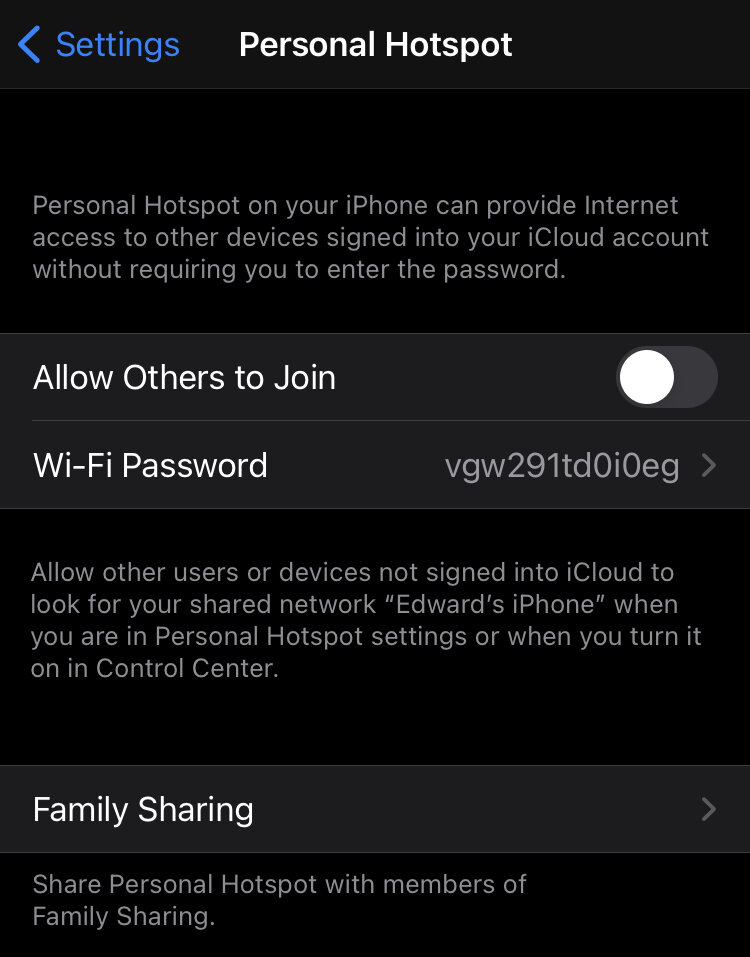
Beyond 2 FA, most users may not realize that their information is being backed up to the cloud. Remember that cloud backup is an easy way for attackers to steal your data. Once you have two-factor authentication enabled on your accounts, ask yourself what you should be backing up to the cloud and where it should be backed up.
Remember that if you choose to trust the backup of your default provider (Apple or Google), you are not in control of your data. In most cases, we now the data is saved unencrypted on those services.
Apple has given police data backed up from an iPhone to icloud
Google, Dropbox and others routinely scan your content looking for malware or copyrighted material
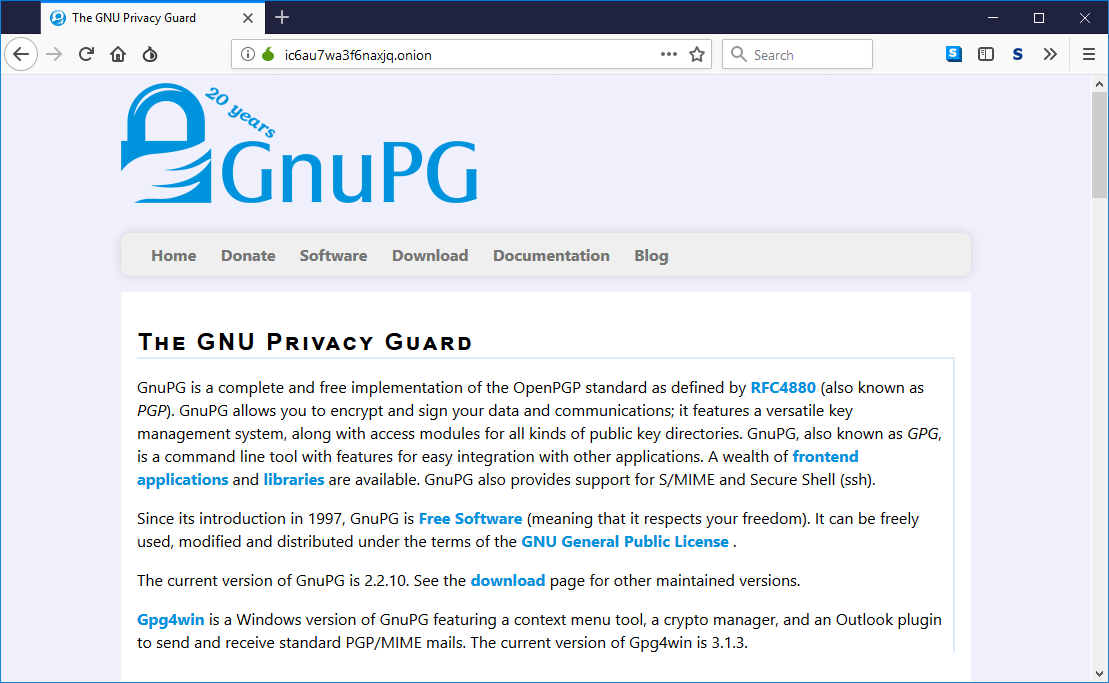
I recommend choosing a secure end-to-end encrypted cloud backup service (if you want to use one). Although there are a bunch in the market, I recommend looking at Sync.com. They offer an end to end encrypted product (using the Trust No One Model). This means that as long as you use two-factor authentication and a long passphrase, your content should be relatively secure.
Your Browser
So your browser is one of the most dangerous apps on your smartphone because it is designed to run code from a remote server (aka a webpage). In the worst-case scenarios, a browser can load a malicious zero-click compromise that would take over your phone without you having to do anything and without you even realizing it. Most of these are non-persistent which is why I recommended regularly rebooting your device earlier.
On Android, I recommend you take a look at a browser called Bromite. Unfortunately due to app store rules, they do not offer a version on the Google Play store and you have to sideload it if you want it. Bromite supports ad-blocking natively and it uses the Ublock Origin model.
It also supports DNS over HTTPS (DOH). You can also enable HTTPS Everywhere and configure it to block unencrypted traffic. You should also disable Javascript and sparingly re-enable it for some sites that you absolutely need but that break without Javascript.
On IOS, I recommend the Brave browser (which is also available on Android but Bromite is more secure). You can download Brave from the Apple AppStore here.
Stalkerware
Stalkerware is a category of badware installed on your device by a third party to spy on you and often to track you.
The EFF is spearheading an initiative to fight Stalkerware (read this) because it is often used to victimize you. Think of it as commercial spyware that covertly steals your data and sends it to the stalker. In some cases, the stalker can be an ex but remember that many companies use Mobile Device Management software that often can perform the same function (normally if the device is owned or is allowed to access the corporate network.) In the case of companies, it is most often done for security reasons. Otherwise (in the private space), it is used to victimize or control someone.
If you are not using a corporate phone and suspect something may be going on (in most cases you won’t realize it), the only way to secure your device is to perform a factory reset and restart the set up from scratch.
Remember that the threat actor (partner, ex, etc.) has to access your device to install the stalkerware so never leave your device unlocked, never leave it unattended and choose a long and complicated passphrase.
Other settings
On IOS, choose to Limit Ad Tracking, instructions can be found here. Choose to reset your Advertising ID (instructions here) periodically.
On Android, choose Opt-Out of Interest-based Ads, instructions can be found here.
Conclusion
I know this was probably a dry and long article for most of you but I needed to get it out. This is a question I receive regularly and I wanted to write about it rather than respond individually to each of you. If you have questions or want to send me a note, do it on twitter (my handle is @ekiledjian).
Hope you found this article interesting and useful.